Page History
...
| Note |
|---|
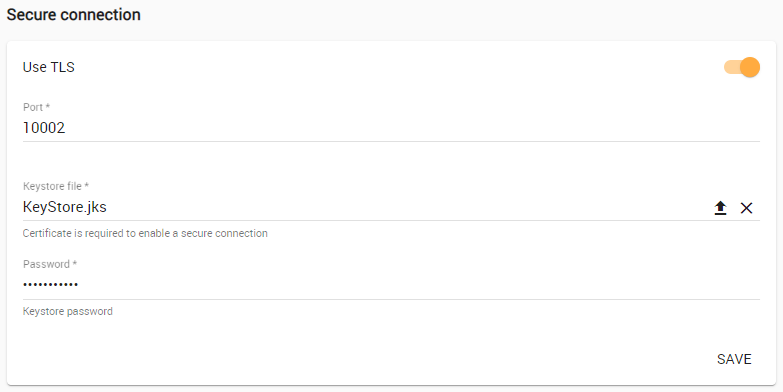
The default port used for secure connection is 10002. |
Enabling TLS protocol in TWCloud (when the option is turned on, the color changes to orange) .
| Warning | ||
|---|---|---|
| ||
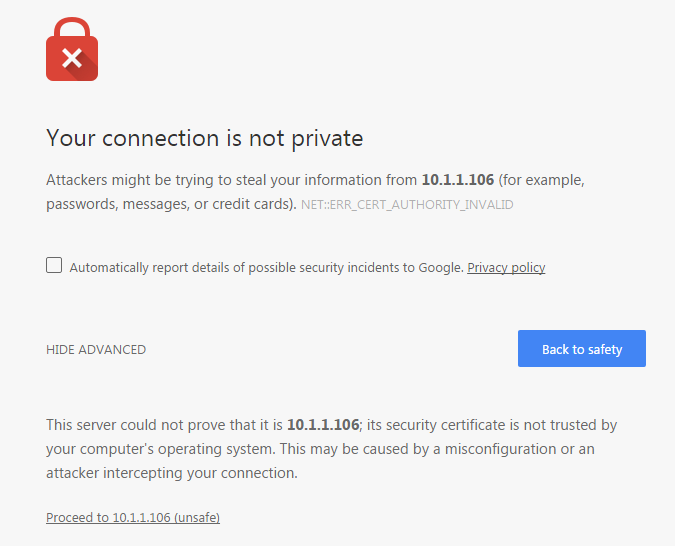
TWCloud Admin uses TLS (Transport Layer Security) as the security protocol to keep any information you enter on TWCloud Admin private and secure. By default, your server generated an TLS certificate and signed it as being valid (self-signed certificate). The self-signed TLS certificate allows a secure connection to be established, but does not verify the authenticity of the server like the TLS certificate issued by a valid Certificate Authority (CA) does. Trusted root certificates are embedded into popular browsers such as Internet Explorer, Firefox, and Chrome. They are used to verify all TLS certificates that the browsers encounters. If a certificate is not signed by one of these roots, the browsers display an error or warning message stating that it is untrusted. Thus, when you try to access the server via the self-signed one, you will get the error or warning in your web browser. The following figure below shows an example of the "TLS certificate not trusted" warning in Chrome. A self-signed TLS certificate error in Google Chrome.This warning tells you the TLS certificate installed on your server was self-signed and cannot be verified by the browser. You may simply let your browser accept it and continue using the server. If you are using Firefox, you can accept it and the error or warning will no longer appear. If you are using Chrome, the error or warning will appear every time you try to access your server. To permanently mitigate this situation to avoid having the self-signed TLS certificate error or warning appear when accessing your server via TLS, it is recommended that you either:
|
...