On this page:
Introduction
There are environments in which the Teamwork Cloud applications need to be fronted by a proxy. The most widespread use case for this is port restrictions whereby the native ports cannot be exposed. Typically, all external traffic is restricted to a single port, such as 443, which is allowed to traverse corporate firewalls or proxies.
In order to configure a proxy, you first need to understand the traffic flows, since each traffic flow needs to be addressed. Teamwork Cloud is composed of 2 services (Webapp and Teamwork Cloud), which need to expose 3 traffic flows (or port bindings) to function.
- Webapp (native port 8443 - http/s)
- Teamwork Cloud
- REST API (native port 8111 - http/s)
- Client Communication (native port 3579 -TCP cleartext or native port 10002 - TLS/TCP encrypted) - 10002 is the default port used by the client and is configured in the Teamwork Cloud Admin Settings page
Additionally, if the FlexNet license server is running on the same instance with the same port constraints, a TCP proxy must be created for it, forwarding to our cameo vendor daemon (native port 1101 - TCP).
Since in TCP/IP you can only bind a single instance of a port to an IP address, the instance will need to have multiple IP addresses in which to bind each traffic flow.
Traffic flows are tied to frontends (the part of the proxy that is exposed to the external world, which receives the requests and forwards to the backends) and backends (handling of the actual requests).
The number of IP addresses required depends on the type of proxying that you configure.
There are 2 types of proxying - TCP (in which case the proxying is done at Layer 4 of the OSI model) or HTTP (in which case the proxying is done at Layer 7 of the OSI).
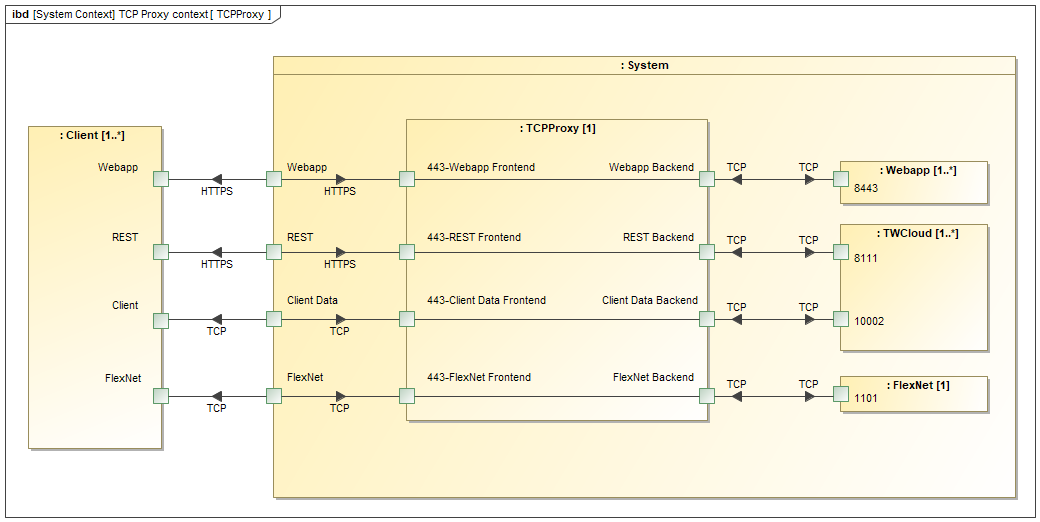
Layer 4 proxying
Layer 4 proxying is the lighter-weight of the 2 methods since it simply forwards incoming packets from the frontend to its associated backend. In this case, you need 3 IP addresses (4 if proxying FlexNet as well) in order to bind to each data flow.
Layer 4 proxy configuration example.
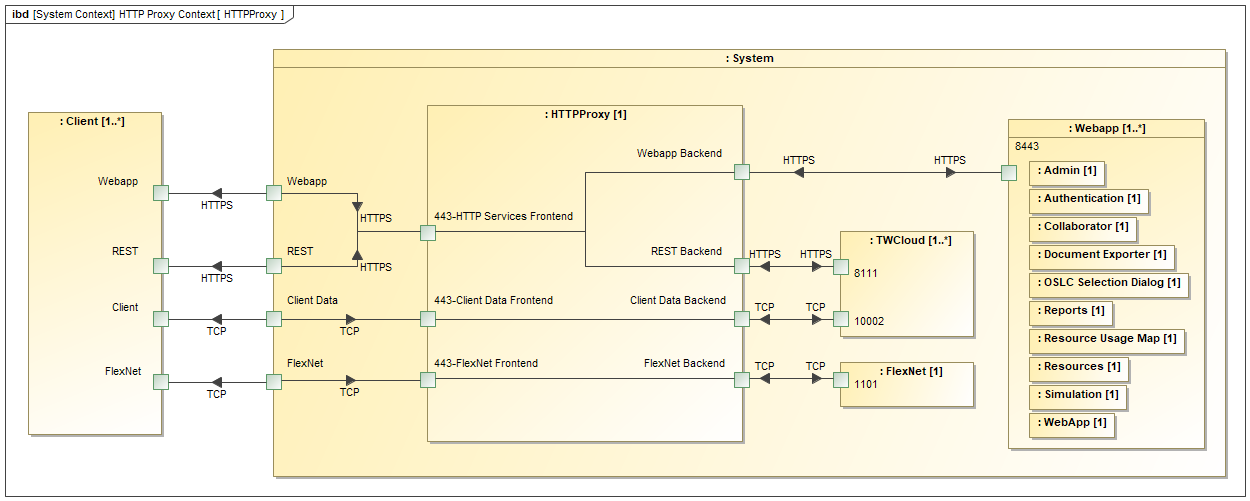
Layer 7 proxying
Layer 7 proxying inspects the actual content of the data coming through the proxy. Therefore, SSL termination takes place at the proxy. In doing so, you can now manipulate the data coming through and take specific actions. Since each of the HTTPS services exposes a path (/webapp for the Teamwork Cloud Admin Console, /osmc for the REST API, and /authentication for the authserver), you can treat the incoming data as a single flow (a single frontend), and have the proxy send the request to the respective backend based on the path of the request.
Layer 7 proxy configuration example.
There are 2 classes of proxies/load balancers. Hardware (such as F5 Big-IP, Cirtix NetScaler) which are external to the application instance, and software (such as nGinx, HAProxy) which can be run externally (on a dedicated instance) or on the same instance as the application.
Proxy configuration
This document will outline how to deploy both Layer 4 (TCP) and Layer 7 Hybrid (HTTPS) proxies utilizing both nGinx and HAProxy. The Layer 7 configuration is a hybrid configuration in that it also includes Layer 4 proxying for the modeling tool client data stream and FlexNet server.
When you initially deploy Teamwork Cloud, you specify a local IP address. This will become the IP address for the Webapp frontend. Keep in mind that the native ports (8443, 8111, client↔Teamwork Cloud port, and the cameo vendor daemon for FlexNet) bind to all interfaces.
In this example, there is an instance with 4 IP addresses - 10.254.254.31 (Webapp), 10.254.254.32 (REST), 10.254.254.34 (client↔Teamwork Cloud), and 10.254.254.35 (FlexNet).
The configurations are the most basic configurations in order for the system to operate. You may add features or change behaviors by modifying these files.
It is noteworthy that in order to simplify all of the aspects of certificates, you should either use a wildcard certificate or one which contains SAN's for all of the public FQDNs and/or IP addresses.
In order to facilitate the deployment, we have prepackaged configuration scripts and template files which will generate the basic configuration files.